Cisco CCNA 1 Simulation v6.0 Test Chapter 9
-
Questions and answers
Resumen
Cisco CCNA 1 Simulation v6.0 Test Chapter 9 Questions and Answers
CCNA 1 Chapter 9 Quiz Questions and Answers. In this simulation, take your test, get your score and share with others!
- Points: 100
- Questions: 23
- Time limit: None
- Allowed attempts: Unlimited
Exam Chapter 9 Questions and Answers CCNA 1 V6.0
Which factor determines TCP window size?
Window is the number of bytes that the sender will send prior to expecting an acknowledgement from the destination device. The initial window is agreed upon during the session startup via the three-way handshake between source and destination. It is determined by how much data the destination device of a TCP session is able to accept and process at one time.
What type of information is included in the transport header?
In a segment, the transport layer header will include the source and destination process, or port numbers. Destination and source physical addressing is included in the frame header. Destination and source logical addressing is included in the network header. Application data is encoded in the upper layers of the protocol stack.
What happens if the first packet of a TFTP transfer is lost?
The TFTP protocol uses UDP for queries, so the TFTP application must implement the reliability, if needed.
What happens if part of an FTP message is not delivered to the destination?
Because FTP uses TCP as its transport layer protocol, sequence and acknowledgment numbers will identify the missing segments, which will be re-sent to complete the message.
Why does HTTP use TCP as the transport layer protocol?
When a host requests a web page, transmission reliability and completeness must be guaranteed. Therefore, HTTP uses TCP as its transport layer protocol.
When is UDP preferred to TCP?
UDP can be used when an application can tolerate some data loss. UDP is the preferred protocol for applications that provide voice or video that cannot tolerate delay.
What information is used by TCP to reassemble and reorder received segments?
At the transport layer, TCP uses the sequence numbers in the header of each TCP segment to reassemble the segments into the correct order.
What is a characteristic of UDP?
UDP has no way to reorder the datagrams into their transmission order, so UDP simply reassembles the data in the order it was received and forwards it to the application.
Which flag in the TCP header is used in response to a received FIN in order to terminate connectivity between two network devices?
In a TCP session, when a device has no more data to send, it will send a segment with the FIN flag set. The connected device that receives the segment will respond with an ACK to acknowledge that segment. The device that sent the ACK will then send a FIN message to close the connection it has with the other device. The sending of the FIN should be followed with the receipt of an ACK from the other device.
What is a characteristic of a TCP server process?
Each application process running on the server is configured to use a port number, either by default or manually, by a system administrator. An individual server cannot have two services assigned to the same port number within the same transport layer services. A host running a web server application and a file transfer application cannot have both configured to use the same server port. There can be many ports open simultaneously on a server, one for each active server application.
What kind of port must be requested from IANA in order to be used with a specific application?
Registered ports (numbers 1024 to 49151) are assigned by IANA to a requesting entity to use with specific processes or applications. These processes are primarily individual applications that a user has chosen to install, rather than common applications that would receive a well-known port number. For example, Cisco has registered port 1985 for its Hot Standby Routing Protocol (HSRP) process.
What does a client do when it has UDP datagrams to send?
When a client has UDP datagrams to send, it just sends the datagrams.
Which two characteristics are associated with UDP sessions? (Choose two.)
Por favor, selecciona 2 respuestas correctas
TCP:
· Provides tracking of transmitted data segments
· Destination devices will acknowledge received data.
· Source devices will retransmit unacknowledged data.
UDP
· Destination devices will not acknowledge received data
· Headers use very little overhead and cause minimal delay.
A host device needs to send a large video file across the network while providing data communication to other users. Which feature will allow different communication streams to occur at the same time, without having a single data stream using all available bandwidth?
Multiplexing is useful for interleaving multiple communication streams. Window size is used to slow down the rate of data communication. Port numbers are used to pass data streams to their proper applications. Acknowledgments are used to notify a sending device that a stream of data packets has or has not been received.
Which three application layer protocols use TCP? (Choose three.)
Por favor, selecciona 3 respuestas correctas
Some protocols require the reliable data transport that is provided by TCP. In addition, these protocols do not have real time communication requirements and can tolerate some data loss while minimizing protocol overhead. Examples of these protocols are SMTP, FTP, and HTTP.
Which two flags in the TCP header are used in a TCP three-way handshake to establish connectivity between two network devices? (Choose two.)
Por favor, selecciona 2 respuestas correctas
TCP uses the SYN and ACK flags in order to establish connectivity between two network devices.
What is the complete range of TCP and UDP well-known ports?
There are three ranges of TCP and UDP ports. The well-know range of port numbers is from 0 – 1023.
A PC is downloading a large file from a server. The TCP window is 1000 bytes. The server is sending the file using 100-byte segments. How many segments will the server send before it requires an acknowledgment from the PC?
With a window of 1000 bytes, the destination host accepts segments until all 1000 bytes of data have been received. Then the destination host sends an acknowledgment.
Refer to the exhibit. Consider a datagram that originates on the PC and that is destined for the web server. Match the IP addresses and port numbers that are in that datagram to the description. (Not all options are used.)
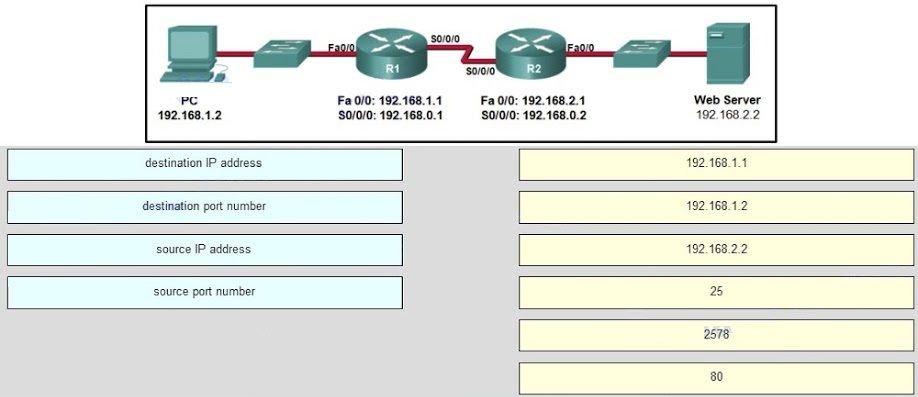
A TCP/IP segment that originated on the PC has 192.168.1.2 as the IP source address. 2578 is the only possible option for the source port number because the PC port number must be in the range of registered ports 1024 to 49151. The destination is the web server, which has the IP address 192.168.2.2, and the destination port number is 80 according to the HTTP protocol standard.
During a TCP session, a destination device sends an acknowledgment number to the source device. What does the acknowledgment number represent?
What does TCP do if the sending source detects network congestion on the path to the destination?
If the source determines that TCP segments are either not being acknowledged or not acknowledged in a timely manner, then it can reduce the number of bytes it sends before receiving an acknowledgment. Notice that it is the source that is reducing the number of unacknowledged bytes it sends. This does not involve changing the window size in the segment header.
What is a socket?
A socket is a combination of the source IP address and source port or the destination IP address and the destination port number.
A host device is receiving live streaming video. How does the device account for video data that is lost during transmission?
When TCP is used as the transport protocol, data must be received in a specific sequence or all data must be fully received in order for it to be used. TCP will use sequence numbers, acknowledgments and retransmission to accomplish this. However, when UDP is used as the transport protocol, data that arrives out of order or with missing segments may cause a momentary disruption, but the destination device may still be able to use the data that it has received. This technology results in the least amount of network delay by providing minimal reliability. Since live streaming video applications use UDP as the transport protocol, the receiver will continue showing the video although there may be a slight delay or reduction in quality.
Comparte tus Resultados:





